
BINARY SHASTRA
Changing The ERA Of Digitalization

Case Study
arrow_back All Case StudiesThe "Shastra" of reliable deployments and secure network environments.

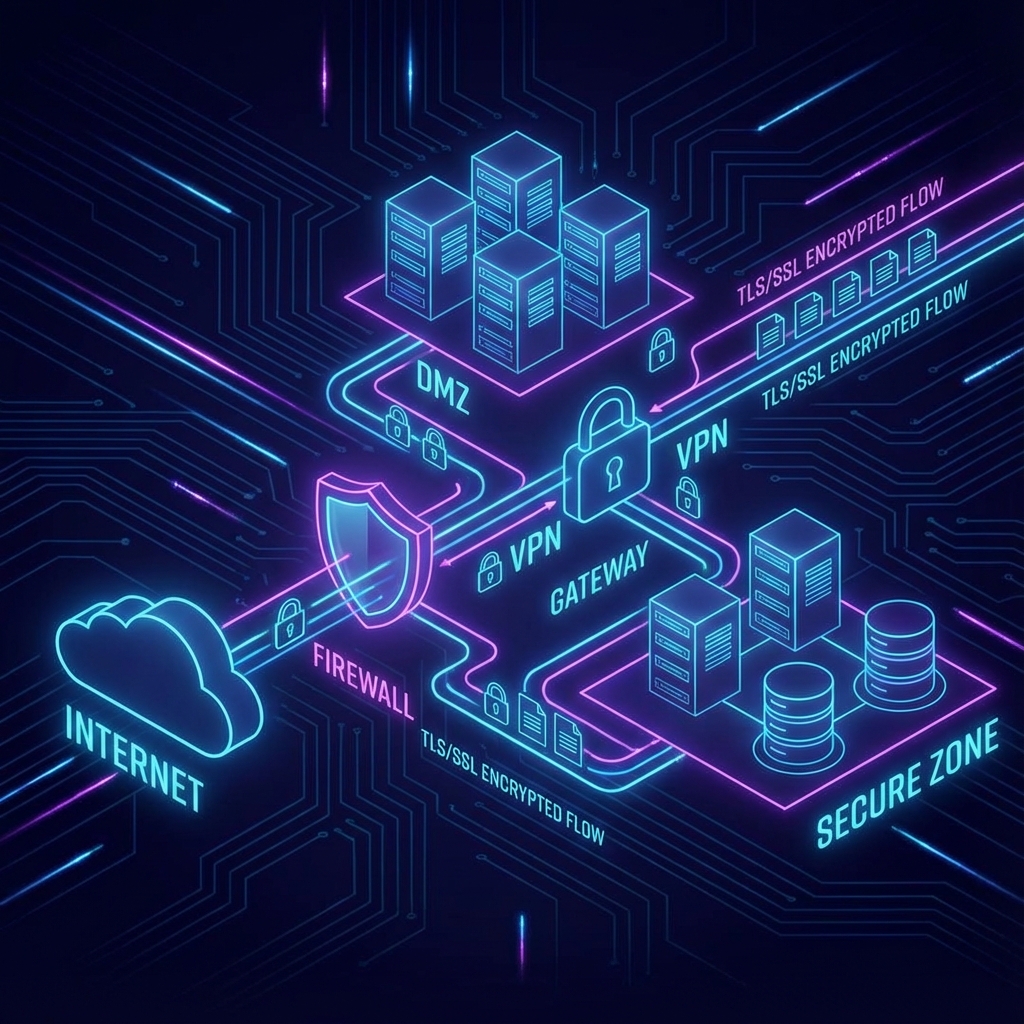
image Fig 1. Secure Network Architecture